Along with growth of the cryptocurrency market as well as blockchain industry, cryptocurrency exchanges are increasingly becoming the targets of attacks. In particular, DDoS attacks are one of the most common forms of cyberattacks.
In the article below, Ecoinomic.io will provide an overview of DDoS attacks on cryptocurrency exchanges.
What is a DDoS attack?
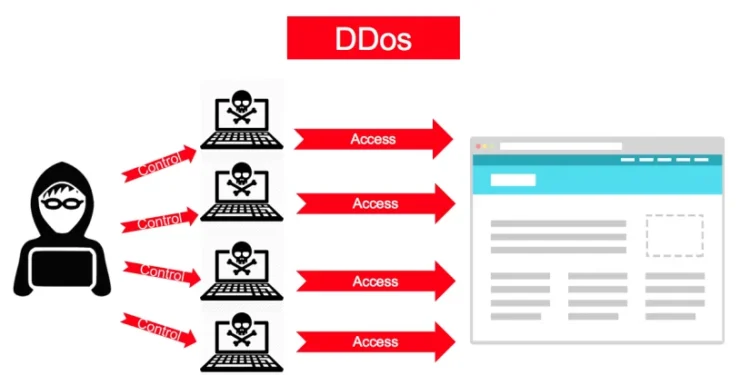
DDoS (Distributed Denial of Service) is a form of attack that prevents normal traffic from valid users to a server, service or web resource.
By overwhelming a targeted server, service or network or surrounding infrastructure with large amounts of Internet traffic, malicious requests, DDoS Attack aims to disrupt the normal traffic and the operation of web resources. That causes the website to overload or crash the server completely.
In some cases, DDoS is a malicious attempt to discredit or damage a competitor’s business.

Classification of DDoS attacks
There are three basic types of DDoS attacks:
- Volume-based or volumetric attacks: control all available bandwidth. For example: DNS amplification – an attacker spoofs a website address and then sends a DNS name lookup request to a DNS server with a spoofed IP address.
- Protocol attacks: exploit all available web server usage or other resources. For example, SYN flood, an attacker sends a website a large number of TCP (transmission control protocol) requests with fake internet protocol addresses.
- Application attacks: target web applications. This is the most serious type of attack despite few attack machines and low traffic rates.
How does a DDoS attack work?
A DDoS attack takes place when the infected computer (bonet) is set up and connected to the entire system, instructing other bots to send spam requests to the target IP address, obstructing and clogging the operation of the network.
Most blockchains have a fixed block size and limit the number of transactions that fit into a block. Attackers can obstruct legitimate transactions added to the chain by sending spam transactions to fill blocks. Therefore, all legitimate transactions will be blocked in the Mempool to wait for the next block.
The differences between DoS and DDoS
In a Denial-of-Service (DoS) attack, an attacker uses a single internet connection to make spoofing requests or exploit network security vulnerabilities.
Meanwhile, DDoS has a larger scale when using thousands (even millions) of connected devices to intercept traffic. The large number of devices used makes it easier for DDoS to succeed.
The impact of DDoS attacks on cryptocurrencies
DDoS attacks on cryptocurrency exchanges and blockchains are becoming more and more popular. In February 2021, cryptocurrency exchange EXMO suffered a DDoS attack and was unable to operate for almost 5 hours. The Solana network also fell victim to a DDoS attack, which went down for about 4 hours in December 2021.
A DDoS attack can take place over a long or short period of time depending on different levels of complexity.
The more decentralized Blockchain, the more secure the network. The blockchain remains active and capable of validating transactions even in the case of some offline nodes. The unaffected Nodes will update the latest data then the interrupted nodes will restore and synchronize the entire data.
How to prevent and mitigate DDoS attacks?
DDoS attacks affect the entire cryptocurrency ecosystem, so it is extremely necessary to implement DDoS prevention and mitigation measures.
The hashrate and the number of nodes directly affect the blockchain’s resistance to DDoS and other related attacks. To maintain stable and secure operations, protocols need to establish nodes with sufficient storage capacity, processing power and network bandwidth as well as provide redundant security solutions for the code of smart contracts.
Besides, transaction filtering is also a method to mitigate attacks in the blockchain system. Most blockchains have a fixed block size and limit the number of appropriate transactions put into the block. Therefore, the block creator has the right to remove and prevent potential spam transactions from entering the ledger to avoid network congestion.
Conclusion
The popularity of cryptocurrencies and blockchain-based financial applications has attracted investors all around the world. However, it also poses potential threat when exchanges fall victim to DDoS attacks.
Therefore, investors need to consider and choose the right trading platform with high level of safety, always raise awareness of risk in the process of making transactions.
>>> Related: How to sign up for Binance account update 2022