Advertisement
In the process of development, the cryptocurrency space has a lot of attacks, causing damage to millions of dollars. Not only does it cause financial damage, but it also affects the confidence of investors. In this article, let’s Ecoinomic.io statistics on the top of the biggest cryptocurrency hacks in the crypto market so far.
Ronin Network Attack
With the growing popularity of Axie Infinity, Ronin was launched as an Ethereum side-chain in February 2021 to provide faster transaction throughput at a more affordable cost for Play-to-earn games. Below is the evolution of the Ronin cyberattack that took place around March 3, 2022.
- On February 23, 2022, 5 of Ronin Chain’s 9 validators were attacked by hackers. Of these, 4 Nodes are run by Ronin Chain and 1 node is operated by a third party under AxieDAO. The attacker then found a backdoor in the gas-free RPC node and obtained the 5th signature.
- After gaining access to the Sky Mavis system (the parent company of Axie Infinity, the developer of the Ronin Chain network) obtain a signature from the Axie DAO validator using the gas-free as mentioned earlier. The project confirmed the signatures in the hacker’s withdrawals that matched the 5 validators mentioned above.
- On March 29, 2022, the new attack was discovered and Ronin Bridge confirmed that 173,600 ETH and 25.5M USDC were withdrawn from the network. After that, Ronin Bridge and Katana DEX were paused. The network’s management team worked with law enforcement agencies, crypto experts, and investors to ensure that all stolen assets were returned.
- On 03/31/2022, the company announced that it will change all previous validators with new validators.

On the hacker’s side, after successfully stealing the above assets, this person transferred 1.05 ETH from the account on Binance as a gas fee and swapped all USDB to ETH via Multichain, and deposited it to the same wallet address (named Ronin Bridge Exploiter). This wallet address has transferred ETH to various personal wallets in order to reduce attention. The ultimate target of the aforementioned ETH is CEX exchanges, including FTX, Crypto.com, and Huobi.
Hackers who have been operating on the network for more than a week have been discovered by the Sky Mavis team. Fortunately, at the time the attack was discovered, an order to withdraw about 5,000 ETH from Ronin Bridge was unsuccessful.
Ronin then suspended Ronin Bridge operations and coordinated with Binance to shut down Ronin Chain deposits and withdrawals to protect Ronin’s assets and prevent hacker withdrawals. After this incident, the developers realized that the current number of authentication nodes was not enough to be safe. Therefore, they decided to increase the number of validating nodes from 5 to 8, that is, enough 8/9 signatures for the transaction to be executed. The unit then partnered with Chainlysis and CrowdStrike to track down the stolen funds and resolve matters related to the investigation.

Poly Network Attack
Poly Network allows connectivity to blockchains through open networks and transparent admission mechanisms in information access, reliability and consistency.
On 10/08/2021, Poly Network announced on Twitter that it had suffered a cross-chain attack and stolen $611M, of which $273M was on Ethereum, $253M on Binance Smart Chain, and $85M on the Polygon network.
Important Notice:
We are sorry to announce that #PolyNetwork was attacked on @BinanceChain @ethereum and @0xPolygon Assets had been transferred to hacker's following addresses:
ETH: 0xC8a65Fadf0e0dDAf421F28FEAb69Bf6E2E589963
BSC: 0x0D6e286A7cfD25E0c01fEe9756765D8033B32C71— Poly Network (@PolyNetwork2) August 10, 2021
A day later, the attacker moved to return the stolen assets. On 2021-08-11, this person sent back $1M USDC on Polygon and then $1.1M worth of BTCB, BUSD, and USDC on Binance Smart Chain. Hackers continue to return SHIB and FEI worth $2.56M. And by 21:00 on the same day, the attacker transferred $119M BUSD and $133M ETH and BTCB to Poly Network’s Binance Smart Chain address.
On 2021-08-12, the attacker refunded over $85M stolen from Polygon network contracts through Binance Smart Chain. Later in the day, the attacker donated $88.2M ETH, $96.9M DAI, and $45.6M WBTC on Ethereum to the Poly Network.
In total, the hacker returned $571M to Poly Network or about 93% of the original stolen funds. Besides, plus the $33M USDT frozen by Tether, the total amount Poly Network has recovered is over $604M.
BNB Bridge Attack
2M BNB was stolen in an attack involving Binance. Specifically, BSC Token Hub, and BNB Bridge – the bridge between Binance Beacon Chain and Binance Smart Chain (now BNB Chain) were mined in 2 transactions, with 1M BNB each. It is estimated that the damage of this cryptocurrency hack amounted to around $570M with 2 million BNB stolen.

Instead of directly selling off BNB and attracting attention, the attacker used the stolen funds as collateral on the Venus Protocol lending platform. After that, they continue to Borrow an amount of about $147M.
This move by hackers has led many to believe that this is not an attack but just a shark money transfer. This is only detected when users start noticing transactions with high slippage and are on the Tether blacklist.
After noticing unusual activity, BNB Bridge had to suspend action for approximately 8 hours to fix the issue, leaving all users unable to access their assets in an emergency and some facing position liquidation.
Hackers promptly dispersed $127M to other networks before losing access to the remaining 1M BNB.
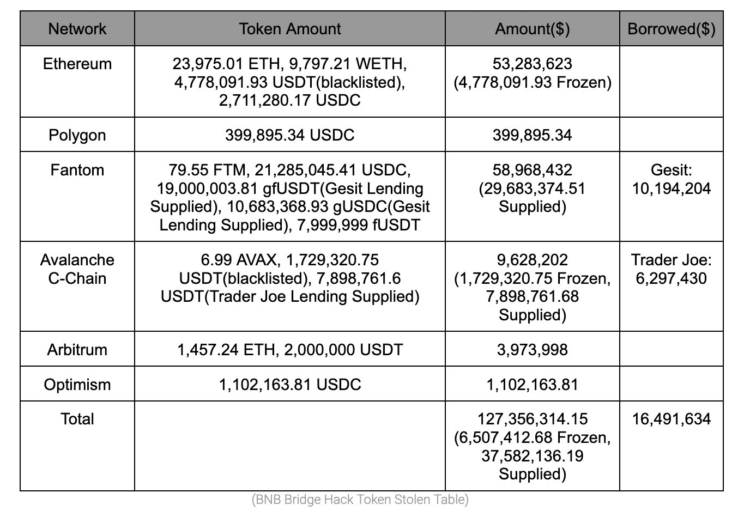
The statistics table for the number of assets transferred is as follows:
Wormhole Attack
A hacker distorted the structure of Solana’s space-time and successfully stole $326M. The platform was then forced to shut down for maintenance and an investigation into the attack.

Specifically, the network was stolen 120K wETH. However, less than 24 hours later, ETH was added to ensure that wETH is supported with a 1:1 ratio on the Solana network.
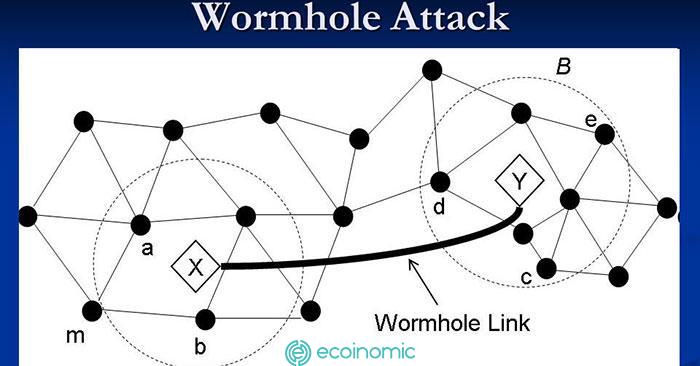
- An attacker can slip through Wormhole’s security system (which is set up to verify shifts between chains) called signatureSet clearance ‘verify_signatures’.
- The ‘verify_signatures’ function of the contract then authorizes the actual verification of the ‘SignatureSet’ for a separate Secp256k1 program. Due to the discrepancy between the ‘solana_program ::sysvar ::architects’ and the ‘solana_program’ Wormhole in use, the contract does not correctly verify the address provided, and the attacker can provide an address containing 0.1 ETH.
- The attacker used an account set up a few hours earlier with serialized instructions corresponding to the Sep256k1 contract and was able to spoof ‘SignatureSet’, call ‘complete_wrapped’, and fraudulently earn 120K whETH on Solana using VAA verification that had been generated in a previous transaction.
- 93,750 ETH was bridged back to Ethereum in 3 trades. The remaining 36K whETH has been liquidated on Solana into USDC and SOL.
Nomad Bridge Attack
Cross-chain bridges are a weakness of DeFi and have always been a “lucrative prey” of attackers, among them, Nomad Bridge was attacked, causing $190M of liquidity to be stolen in just 2.5 hours.
Nomad bridge is a cross-chain project developed with the goal of increasing interoperability between blockchains with the core product being the Nomad token bridge. The platform allows users to move assets freely via Polkadot’s Moonbeam parachain, Ethereum, Evmos, and Milkomeda.

Collateral damage from unsupported assets also severely affected nomad-dependent chains. Moonbeam’s TVL, EVMOS, and Milkomeda were all affected.
Cryptocurrency hacks with other major losses
In addition to the aforementioned attacks, the crypto space has recorded countless other attacks with losses of millions of dollars. Here are some typical attacks:
- BitMart Attack – $196,000,000
- Beanstalk Attack – $181,000,000
- Wintermute Attack – $162,300,000
- Attack Compound – $147,000,000
- Attack Vulcan Forged – $140,000,000
- Attack Cream Finance – $130,000,000
- Badger Attack – $120,000,000
- Harmony Bridge Attack – $100,000,000
- Attack Mirror Protocol – $92,000,000
- Fei Rari Attack – $80,000,000

Conclusion
The crypto space has thrived for about a decade or so. The development of cryptocurrencies as well as blockchain projects has become the target of cybercriminals. Listing cryptocurrency attacks, we see the important role of cybersecurity and confidentiality in this space.
Entering the market, users cannot expect the network or managers to “keep” assets for them. In the future, cryptocurrency hacks will definitely happen, so cultivating knowledge and taking precautions is the most important thing. Ecoinomic.io wish you the best experience with this potential space.
See more: What is a Private Key And Passphrase? Crypto Account Security Tools