Advertisement
What is a digital signature?
It is a mathematical diagram to prove the authenticity of a message or digital document, ensuring the subject is not altered or tampered with (integrity.)
Giving the recipient reason to believe that the message was created by a known sender and was not altered during shipping. Therefore, they are equivalent to traditional handwritten signatures in many respects. If It was done correctly, is often harder to forget than handwriting.
How to use a digital signature
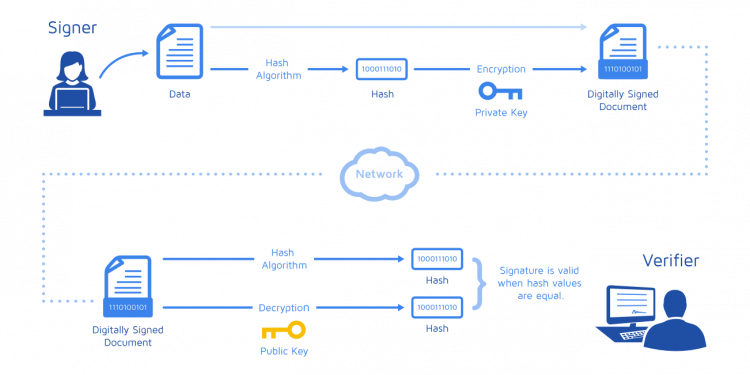
Using public key cryptography, in which encryption and decryption are done using public and Private Key pairs. Messages sent through an insecure channel, are made in a way that gives the recipient reason to believe that the message sent by the sender is requested. Signature diagrams are used based on cryptography and must be done properly to be effective.
To sign a message, the sender uses the software to create a harsh hash of the message, which is then encrypted with their private key. To verify the message, the encrypted hash needs to be decrypted using the sender’s public key. Then a second hash of the message is created; if this hash matches the decoded hash, the message is valid.
See also: Crypto’s Uses And Misuses: Quarrel Between Reuters And Binance
Algorithmic structure of the Digital Signature diagram
Usually consists of three algorithms:
- An algorithm creates a randomly selected key that identifies a private key from a set of possible private keys. The algorithm exports to the private key and the corresponding public key.
- A signing algorithm, provided with a message and a private key, creates a signature.
- A signature verification algorithm, provided for a message, public key and signature, accepts or rejects the message’s authentication request.
The use of a digital signature
Authenticity
While messages can often include information about the entity sending the message, that information may not be accurate. They can be used to authenticate the source of messages. When ownership of the secret key is tied to a particular user, a valid signature indicates that the message was sent by that user. The importance of high confidence in sender authenticity is particularly evident in the financial context.
Integrity
They help ensure that the message’s content is not changed during transmission. If a message is signed electronically, any changes in the letter after signing will invalidate the signature. Furthermore, there is no way to modify a message and its signature to create new content with a valid signature, because this is still considered mathematically unfeasible.
No rejection
Not refusing, or more specifically not denying origin, is an important aspect of digital signatures. According to this property, an entity that has signed some information cannot deny signing it. Likewise, access to the public key doesn’t allow a fraudulent party to forge a valid signature. This is in contrast to symmetrical systems, in which both the sender and receiver share the same secret key, and therefore in disputes, the third party cannot determine which entity is the real source of information.

Xem thêm: What Is Proof Of Work And How Does PoW Work In Crypto?
Compare digital signature and electronic signature
They are often used to make electronic signatures, a broader term that refers to any electronic data that carries the intent of the signature, but not all electronic signatures use them. Electronic signatures simply refer to any digital trademarks intended to represent the signature. In some countries, including the United States, India and members of the European Union, electronic signatures have legal significance. However, laws relating to electronic signatures do not always apply to them.
Conclusion
It helps secure important content and messages and prevents others from tampering with self-seeking purposes. If the signed content is changed unexpectedly, It will be invalidated and invalidated, and both sender and receiver will be alerted to this change. In short, It brings many benefits to businesses and agencies in signing legally binding commercial documents.